WASHINGTON -- Six Russian military intelligence officers have been charged in the United States with carrying out cyber-attacks across the globe, the US Justice Department announced on Monday (October 19).
The six, all members of Unit 74455 of the Russian Main Intelligence Directorate (GRU), were identified as Yuriy Sergeyevich Andrienko, 32; Sergey Vladimirovich Detistov, 35; Pavel Valeryevich Frolov, 28; Anatoliy Sergeyevich Kovalev, 29, Artem Valeryevich Ochichenko, 27; and Petr Nikolayevich Pliskin, 32.
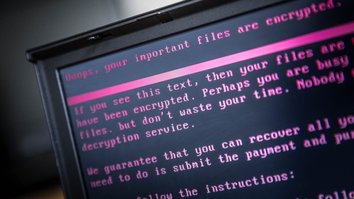
They are accused of staging 2015 and 2016 cyber-attacks on Ukraine's power grid, the 2017 French elections and the 2018 Winter Olympic Games in South Korea, as well as a 2017 malware attack called "NotPetya" that infected computers of businesses worldwide, causing almost $1 billion in losses to three US companies alone.
In addition, they allegedly targeted international investigations into the nerve-agent poisoning in England of Russian former double agent Sergei Skripal and his daughter, as well as waging cyber-attacks on media outlets and parliament in Georgia.
![Four alleged Russian GRU agents are shown arriving in Amsterdam, the Netherlands, April 10, 2018. Dutch authorities later expelled them for allegedly trying to hack the OPCW, the chemical weapons watchdog. The timing of the attempted hack was significant as Moscow attempted to delay OPCW access to a chemical weapon attack in Douma, Syria, giving the Kremlin time to tamper with the site. [Dutch Defence Ministry]](/cnmi_ca/images/2020/10/20/26642-jeff-585_329.jpg)
Four alleged Russian GRU agents are shown arriving in Amsterdam, the Netherlands, April 10, 2018. Dutch authorities later expelled them for allegedly trying to hack the OPCW, the chemical weapons watchdog. The timing of the attempted hack was significant as Moscow attempted to delay OPCW access to a chemical weapon attack in Douma, Syria, giving the Kremlin time to tamper with the site. [Dutch Defence Ministry]
Six officers were responsible for "the most disruptive and destructive series of computer attacks ever attributed to a single group", said US Assistant Attorney General John Demers.
Members of the same GRU unit previously had been charged with seeking to disrupt the 2016 US elections, said Demers.
The charges include conspiracy to conduct computer fraud and abuse, conspiracy to commit wire fraud, wire fraud, damage to protected computers, and aggravated identity theft, covering four years of malicious cyber activity from 2015 to 2019.
'Petulant child'
The group's attacks spanned France, Georgia, the Netherlands, Republic of Korea, Ukraine, the United Kingdom, and the United States.
The defendants launched destructive malware attacks against the electric power grid in Ukraine in December 2015 and December 2016, said Demers.
"These were the first reported destructive malware attacks against the control systems of civilian critical infrastructure," he said.
"These attacks turned out the lights and turned off the heat in the middle of the Eastern European winter, as the lives of hundreds of thousands of Ukrainian men, women and children went dark and cold."
The defendants conducted "hack-and-leak" campaigns (meant to steal confidential information and then release it to the public domain) against French President Emmanuel Macron's political party and against local French governments prior to the 2017 elections, said the Justice Department.
The 2018 Pyeongchang Winter Olympics in South Korea were targeted after the International Olympic Committee (IOC) banned Russian athletes from participating under their own flag because of government-sponsored doping efforts, said Demers.
"Their cyber-attack combined the emotional maturity of a petulant child with the resources of a nation state," he said, adding that the culprits attempted to pin it on North Korea.
The group carried out internet reconnaissance missions against targets linked to the Tokyo Olympics, before the IOC postponed the games until 2021 because of the coronavirus pandemic, said British officials October 19.
In April 2018, "spear phishing" campaigns (meant to deceive email recipients into giving up confidential information) were launched against investigations being carried out into the Skripal poisoning by the multi-national Organisation for the Prohibition of Chemical Weapons (OPCW) and the United Kingdom's Defence Science and Technology Laboratory.
In Georgia, a spear phishing campaign was launched in 2018 against a major media company, and in 2019 hackers made efforts to compromise the computer network of the country's parliament, according to the Justice Department.
Meanwhile, the 2017 NotPetya attacks slammed businesses and critical infrastructure worldwide, and US victims included hospitals, a subsidiary of delivery giant FedEx and a pharmaceutical manufacturer.
Malicious and irresponsible
The indictment is the latest evidence of Russia's widespread hacking and disinformation tactics.
"No country has weaponised its cyber capabilities as maliciously or irresponsibly as Russia, wantonly causing unprecedented damage to pursue small tactical advantages and to satisfy fits of spite," Demers said.
In July, British officials accused Russian intelligence of spearheading online attacks on various organisations involved in COVID-19 vaccine development to steal information and intellectual property.
"At the time that the world has come together to try and tackle COVID-19... I think it's outrageous and reprehensible that the Russian government is engaged in this activity," British Foreign Secretary Dominic Raab said at the time.
Earlier in May, German Chancellor Angela Merkel voiced frustration with the Kremlin's attempts to hack her personal accounts and to spy on leading politicians.
Those incidents came as thousands of Russian-linked social media accounts launched a co-ordinated effort to spread conspiracy theories about the coronavirus as part of a campaign to discredit Western healthcare systems.
In May, Facebook took down scores of Russian-based social-media accounts running influence campaigns set up to disrupt elections and society in general around the world. In February, Facebook purged dozens of accounts linked to Russian military intelligence trying to stir up ethnic tension.
The social-media platform in September uncovered a budding Kremlin-linked campaign to fuel political chaos in the United States, removing a network of 13 Facebook accounts and two pages posing as journalists and targeting left-wing progressives violating its policy against "foreign interference".

![A poster showing six wanted Russian military intelligence officers is displayed as US Attorney for the Western District of Pennsylvania Scott Brady (R), accompanied by US Assistant Attorney General John Demers (L), speaks at a news conference in Washington October 19. [Andrew Harnik/POOL/AFP]](/cnmi_ca/images/2020/10/20/26640-000_8tf2kf-585_329.jpg)






After reading these absolutely baseless articles filled with high-quality nonsense, you can't help thinking it took a brain damaged like Klichko's to write this article.
Reply1 Comment(s)